Lessons learned from 2016, but U.S. faces new election threats
It’s been more than three years since Russia's sweeping and systematic effort to interfere in U.S. elections through disinformation on social media and stolen campaign emails.
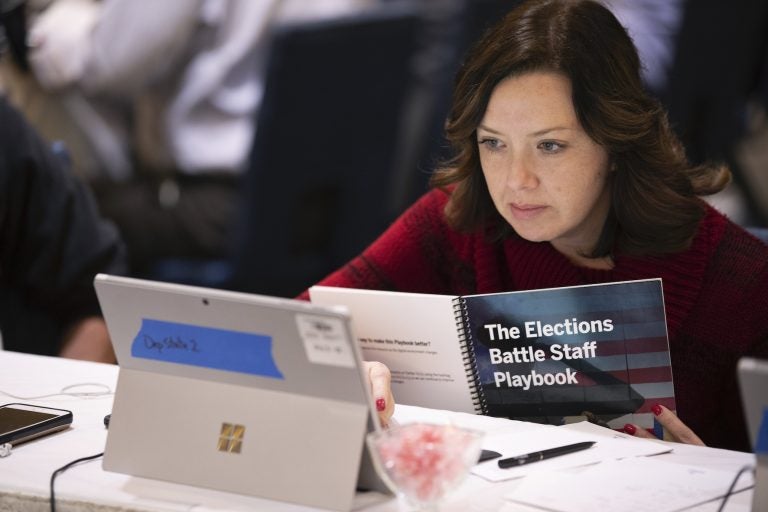
Mandy Vigil, from New Mexico, works during an exercise run by military and national security officials, for state and local election officials to simulate different scenarios for the 2020 elections, Monday, Dec. 16, 2019, in Springfield, Va. (Alex Brandon/AP Photo)
It’s been more than three years since Russia’s sweeping and systematic effort to interfere in U.S. elections through disinformation on social media, stolen campaign emails and attacks on voting systems. U.S. officials have made advances in trying to prevent similar attacks from undermining the 2020 vote, but the potential threats have increased and some old problems have not been addressed. A look at what has changed since 2016 and what has not.
The Threat
THEN: U.S. intelligence agencies say Russia was the only nation that significantly interfered in the 2016 election. Russia’s activities shouldn’t have come as a surprise. Russia is believed to have interfered in Ukraine’s 2014 vote. Russia’s 2016 goals, according to an assessment by the U.S. intelligence agencies, were to add to the divisiveness in American society, undermine faith in the democratic process and harm Democrat Hillary Clinton’s White House candidacy and potential presidency.
NOW: The threat has expanded considerably. U.S. intelligence chiefs say potential threats aren’t just from Russia, but also from China, Iran and North Korea. In addition, there have been indications that hostile foreign governments might disguise their attacks to make them appear to be caused by other hackers. Campaigns and state and local election systems remain attractive targets, and social media is still a convenient method for sowing divisions.
___
Threat Awareness
THEN: U.S. officials were ill-prepared for Russian intelligence officers to hack Democratic emails and distribute them to WikiLeaks. In addition, the covert Russian social media campaign aimed at spreading disinformation among American voters was unprecedented and largely undetected until after the election. Campaigns underestimated the threat. State and local election officials were unaware that they were on the front lines of defending U.S. democracy.
NOW: U.S. intelligence chiefs have tried to reassure the public that securing U.S. elections from outside interference is a top priority. That’s despite President Donald Trump’s comments dismissing claims of Russian interference in the 2016 election and his assertion that he would be open to receiving information on his opponents from foreign governments. FBI Director Chris Wray frequently warns of foreign interests meddling in American politics. He has established a task force aimed at countering foreign hacking and disinformation campaigns. State and local election officials repeatedly highlight the work they are doing to boost election security, such as training, cybersecurity improvements and collaborations with federal officials.
___
Federal Engagement
THEN: Before 2016, there were no clear communication channels between federal authorities and the states, which have primary responsibility for elections. When federal officials began to suspect election systems were being targeted in 2016, they communicated with some state officials but not necessarily those overseeing elections. Some state election officials did not learn their systems had been targeted by Russia until late 2017.
NOW: The Department of Homeland Security has strengthened relationships with state and local election officials. They’ve offered free cybersecurity services, such as risk assessments and vulnerability scanning, and created an information-sharing group. They’ve granted security clearances to state election officials so they can receive threat intelligence. They’ve also sent equipment to states to help detect malicious cyberactivity. This was largely made possible after then-Homeland Security Secretary Jeh Johnson in January 2017 designated election systems as “critical infrastructure,” on par with power plants, banks and dams. Despite initial concerns about the designation, state and local officials now largely praise federal efforts to support them.
___
Cybersecurity in the States
THEN: Before the 2016 election, state election offices were mostly focused on ensuring orderly elections and that voting-related equipment functioned properly. When Russia breached Illinois’ voter registration system and searched for vulnerabilities in state election systems across the country, it underscored how outmatched state and local election officials were. The threat was not isolated to voting machines, but included internal networks, voter registration systems, electronic pollbooks and vote reporting websites.
NOW: States have been scrambling since 2016 to increase their cyberdefenses, upgrade voting systems and train local election officials. They received $380 million in federal money in 2018, though cybersecurity advocates say that wasn’t enough. Last month, Congress approved an additional $425 million to states, although it’s likely too late for these funds to be spent replacing old or vulnerable voting equipment. But the money can be used quickly for cybersecurity personnel, training and audits to ensure the accuracy of election results. While the 2018 elections occurred without any major incidents, experts say the true test of how resilient state and local election systems are will be 2020.

___
Voting machines
THEN: Much of the voting equipment in use in 2016 was purchased in the early 2000s amid efforts to update election administration following the “hanging chad” fiasco of the 2000 presidential election. But that fix created new problems. Some new voting machines had touchscreens and did not produce an auditable paper record of every vote cast. That meant there was no way to ensure these machines were counting votes accurately. Researchers have also shown these machines are vulnerable to hacking. In 2016, 20 percent of U.S. voters, some 27.5 million people, used these electronic voting machines.
NOW: Some state and local election offices have been upgrading old and vulnerable voting equipment. But as many as 12 percent of voters nationally, or an estimated 16 million people, will continue to use electronic-only machines, according to an analysis by the Brennan Center for Justice at NYU’s Law School. A Senate report urged states to ensure all ballots are cast on machines that produce paper records allowing voters to verify their selections. But legislation that would require states to make the switch has stalled. Meanwhile, concerns have been raised about new touchscreen voting machines known as ballot-marking devices. Although these machines produce a paper record, there are concerns voters will not verify their selections to ensure they are accurate, that the software could be tampered with or a ballot programming error could occur.
___
Vendor security
THEN: In 2016, three private companies dominated the voting equipment industry and faced minimal federal oversight. In addition to manufacturing voting machines and equipment, the companies — Election Systems & Software, Dominion Voting Systems and Hart InterCivic — also provide election management and vote-tallying systems for many of the nation’s 10,000 voting jurisdictions.
NOW: Nothing has changed when it comes to oversight of the industry. Vendors are still not required to submit their voting systems or corporate networks to independent, third-party testing for vulnerabilities. Their voting systems are certified by labs under a voluntary system administered by the U.S. Election Assistance Commission. Security specialists say this testing is inadequate and note the commission’s guidelines have not been substantially updated since 2005. Vendors are not required to report cybersecurity breaches involving their systems. Some vendors have submitted their systems to a government lab for security testing, although the results of those tests have not been made public. ES&S has said it has also partnered with Homeland Security to install an intrusion detection system on its voter registration systems.
___
Safeguarding campaigns
THEN: Russia largely caught political organizations off guard. The 2016 attacks were relatively low-tech, involving hundreds of spearfishing emails. All it took was a few people clicking on the wrong email and providing their login information. That opened the door to sensitive documents and emails being stolen and released publicly.
NOW: Campaigns have been largely reticent to detail cybersecurity efforts since 2016, so it’s difficult to gauge their abilities to prevent attacks. Certainly, awareness of the threat is higher, and Homeland Security and technology companies have offered resources to help campaigns. Candidates have also been receiving advice from the Republican and Democratic national committees, which say they are in regular communication with federal officials and are focused on implementing basic security protocols, including steps to prevent phishing attacks.
___
Social media/Disinformation
THEN: The 2016 election was marred by Russian attempts to use fake accounts on social media to increase polarization among Americans. A Senate report said Russian operatives masqueraded as Americans, using targeted ads, intentional false news stories and social media to interact and attempt to deceive millions in the U.S. Both law enforcement and social media companies were ill-prepared to identify the threat, let alone address it.
NOW: Since 2016, social media platforms have invested in efforts to combat misinformation, identify online impostors and root out foreign interference in domestic elections. Twitter stopped accepting political ads, while Facebook began verifying the identity of ad buyers in 2018 and further tightened its rules last year. Google has made it harder for advertisers to target audiences based on specific characteristics such as their voting record or political affiliation. The changes haven’t satisfied critics who say the platforms and their policies, and a lack of action by the government, leave the U.S. open to additional disinformation campaigns in 2020 — from both foreign and domestic sources.
___
Public disclosure
THEN: In 2016, there was no federal law to compel a federal agency or state and local government to disclose the breach of an election system, and a federal policy shielded the identity of all cyber victims regardless of whether election systems are involved. That meant state officials wouldn’t necessarily find out if an electoral system in one of its counties had been attacked and could certify elections without realizing there had been problems.
NOW: There have been no changes to federal law. Even now, the public still doesn’t know which Florida counties were breached by Russian agents in 2016. In a step toward addressing that secrecy, the Trump administration last year released a framework for notifying victims and the public of cyberattacks during the 2020 election. Decisions about whether to provide notification would take into account the need to avoid undermining investigations and to protect sources and methods. Also, the FBI now plans to notify state election officials in the event a local system is breached, but will not release this information to the public.
___
Associated Press writers Eric Tucker and Colleen Long in Washington; Frank Bajak in Boston, and David Klepper in Providence, Rhode Island, contributed to this report.
WHYY is your source for fact-based, in-depth journalism and information. As a nonprofit organization, we rely on financial support from readers like you. Please give today.